134.If you want to get the driver‘s( ), you should take some courses first in the traffic school.
A. license
B. certificate
C. passport
D. permission
https://www.shititong.cn/cha-kan/shiti/0005fce5-7636-9ff8-c039-62ee46700007.html
点击查看答案
1、Passage 19Throughout her working life, a ship — like a motorcar — must be serviced regularly if she
is to remain efficient. After a period at sea she must be overall checked and any necessary repairs
must be made. There are also instances when a ship must be converted from being one kind of
carrier to another. Most of today‘s oil, for example, is carried by huge super-tankers. The smaller
tankers, many of which are still in good condition, can be converted into bulk carriers(散货船)
for the transport of sugar, coal or ore.
Conversion or repair work is carried out in a dry dock, a huge hole cut into the ground and
lined with concrete. At one end are large gates separating the dock from the river or sea. When
these gates are opened, water pours into the dock and fills it. A ship can then enter the dock, where
it is carefully fastened in an upright position.When the ship is positioned inside the dock, the gates are closed and the water is pumped out.
The vessel slowly settles on to wooden blocks. Wooden supporters are put in position between the
ship and the sides of the dock to prevent her from rolling over. Great care is taken to make sure
that the ship rests evenly on the keel(龙骨)blocks to prevent damage being done.
As soon as the ship is firmly positioned, repair or conversion work can begin on her body or
superstructure.
5. According to the passage, how is a ship kept upright in a dry dock?
A. It is lined with concrete.
B. It is placed on keel blocks.
C. It is fastened to the shore.
D. It is supported with pieces of wood.
https://www.shititong.cn/cha-kan/shiti/0005fce5-7636-9058-c039-62ee46700002.html
点击查看答案
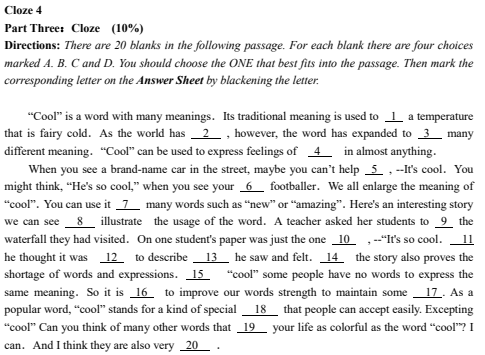
6、

19、
A. effective
B. sensitive
C. ordinary
D. careful
https://www.shititong.cn/cha-kan/shiti/0005fce5-7636-b380-c039-62ee46700008.html
点击查看答案
5、

16、
A. mix
B. combine
C. join
D. associate
https://www.shititong.cn/cha-kan/shiti/0005fce5-7636-af98-c039-62ee46700015.html
点击查看答案
9、
3、
A. Then
B. But
C. So
D. Also
https://www.shititong.cn/cha-kan/shiti/0005fce5-7636-b768-c039-62ee4670000f.html
点击查看答案
1、Passage 20Clifford Stoll ran a computer system in Berkelely, California. As a system administrator, he
kept a close eye on the records. One day, Stoll found something strange in the payment record.
There was a 75 cents mistake. One of the thousands of users had used the system for 75 worth of
time and not paid for it.
It might sound like very little money to worry about. But that 75 cents was the first clue Stoll
had to a much bigger problem — that a hacker(黑客)had broken into Stoll‘s computer system.
Who was it? Stoll spent the next year trying to find out. During that time the hacker used the
system in Berkelely as a starting point to break into military computer systems all over the United
States.
Stoll had to keep track of the hacker‘s activities on the computer without the hacker‘s
knowing someone was watching him. Stoll even made up huge files of false information so the hacker would have lots to read. When the hacker spent long time reading, the telephone company
was able to trace the lines. After a year, the hacker was traced back to his computer — in
Germany. He was later caught by the German police.
1. The passage is mainly about ________.
A. how Stoll ran his computer system
B. how a hacker used the computer system without paying the money
C. how a hacker was tracked down by Stoll
D. how the police caught a hacker by surprise
https://www.shititong.cn/cha-kan/shiti/0005fce5-7636-9058-c039-62ee46700003.html
点击查看答案
4、
4、
A. satisfaction
B. interest
C. sense
D. interesting
https://www.shititong.cn/cha-kan/shiti/0005fce5-7636-abb0-c039-62ee46700019.html
点击查看答案
9、
10、
A. acceptable
B. responsible
C. reasonable
D. accountable
https://www.shititong.cn/cha-kan/shiti/0005fce5-7636-b768-c039-62ee46700016.html
点击查看答案
1、Passage 20Clifford Stoll ran a computer system in Berkelely, California. As a system administrator, he
kept a close eye on the records. One day, Stoll found something strange in the payment record.
There was a 75 cents mistake. One of the thousands of users had used the system for 75 worth of
time and not paid for it.
It might sound like very little money to worry about. But that 75 cents was the first clue Stoll
had to a much bigger problem — that a hacker(黑客)had broken into Stoll‘s computer system.
Who was it? Stoll spent the next year trying to find out. During that time the hacker used the
system in Berkelely as a starting point to break into military computer systems all over the United
States.
Stoll had to keep track of the hacker‘s activities on the computer without the hacker‘s
knowing someone was watching him. Stoll even made up huge files of false information so the hacker would have lots to read. When the hacker spent long time reading, the telephone company
was able to trace the lines. After a year, the hacker was traced back to his computer — in
Germany. He was later caught by the German police.
5. Why did Stoll make up huge files of false information?
A. He wanted to give the hacker a lesson.
B. It would help the telephone company trace the line.
C. It would give the police more time to find out the hacker.
D. He could watch the hacker‘s activities more closely.
https://www.shititong.cn/cha-kan/shiti/0005fce5-7636-9058-c039-62ee46700007.html
点击查看答案
200.( )the children to bed, she began to correct the students‘ exercises.
A. Sending
B. Being sent
C. Sent
D. Having sent
https://www.shititong.cn/cha-kan/shiti/0005fce5-7636-a3e0-c039-62ee46700023.html
点击查看答案








 19、
19、
 16、
16、
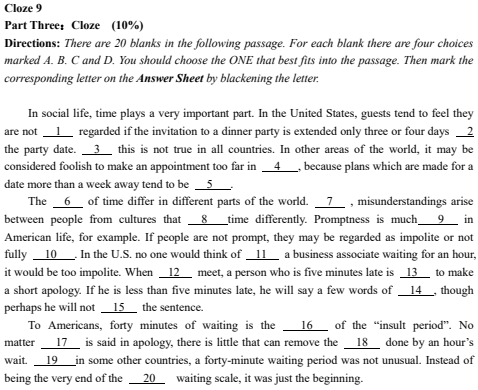 3、
3、
 4、
4、
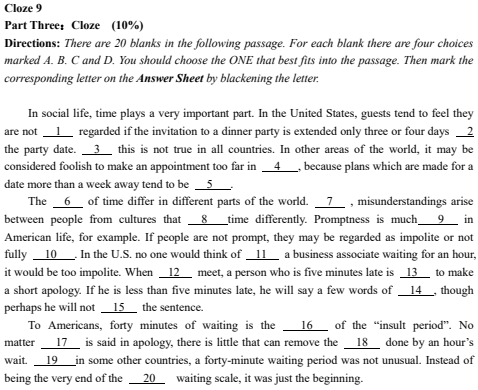 10、
10、